MIT 6.S895 (Spring 2024)
Quantum Cryptography
Announcements
- [2/23] Problem Set 1 is posted here, due midnight on Friday March 8th. Submit your solutions on Canvas.
- [2/13] Tuesday's class is canceled as MIT is closed for the snowstorm!
- [2/6] Problem Set 0 is posted here. This is only so you can calibrate your understanding of the quantum basics. You do not need to turn it in.
- Lecture videos are available at this page. You need to have MIT certificates to access the videos.
Course Description
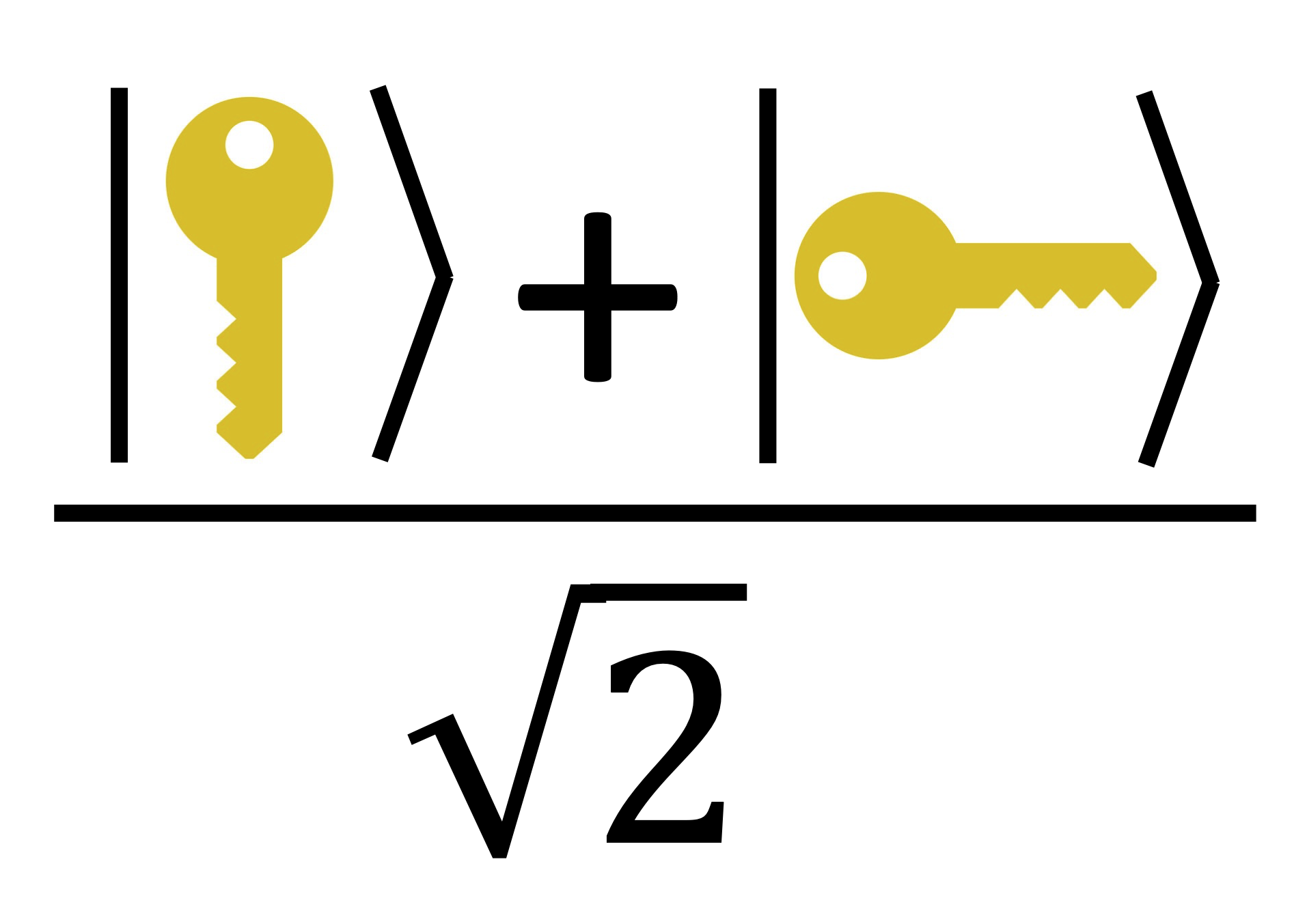
This course is an introduction to the many ways quantum computing and cryptography intersect. Topics will include uniquely quantum cryptographic primitives such as quantum key distribution and quantum money, post-quantum cryptography (classical cryptography that is secure against quantum attackers), the use of cryptography in verifying quantum devices, as well as unclonable cryptography. Some familiarity with both quantum computing and cryptography is assumed.The audience is graduate students interested in quantum computing, cryptography, or more broadly the theory of computing. Students are expected to have some familiarity with the basic notions of quantum computing and cryptography, and to be mathematically mature (comfortable with writing proofs, and with linear algebra and basic notions in group theory and number theory).
Prerequisites: Students are expected to be familiar with the basics of quantum information and computation (at the level of 6.6410, Quantum Computation, or 6.6420, Quantum Information Science) and the basics of cryptography (at the level of 6.5620 Foundations of Cryptography) or obtain the permission of instructors.
Course Information
| INSTRUCTORS |
Anand Natarajan Email: anandn at mit dot edu Vinod Vaikuntanathan Email: vinodv at mit dot edu |
| LOCATION AND TIME | Tuesday and Thursday 11:00-12:30pm in 45-102 (in the new Schwarzman College of Computing building). |
| TAs |
Tina Zhang Email: tinaz at mit dot edu Office hours: TBD. Location: TBD. |
| RESOURCES |
The main references will be the course materials including lecture notes, slides and/or videos.
We will also post relevant papers after every lecture.
Here are a few supplementary references for the entire course material.
Lecture notes
|
| PIAZZA | We will use Piazza for class communication. Please ask your questions there, so that other students can see the questions and answers. |
| ASSIGNMENTS AND GRADING | Grades will be determined based on 2 problem sets (20% each) and a final project, including a project presentation and a writeup (60%). The final projects can be done in groups of at most two. |
| COLLABORATION POLICY | Collaboration is permitted and encouraged in small groups of at most three students. You are free to collaborate in discussing answers, but you must write up solutions on your own, and must specify in your submission the names of any collaborators. Do not copy any text from your collaborators; the writeup must be entirely your work. Do not write down solutions on a board and copy it verbatim into Latex; again, the writeup must be entirely your own words and your own work and should demonstrate clear understanding of the solution. Additionally, you may make use of published material, provided that you acknowledge all sources used. |
Schedule (tentative and subject to change)
| Lecture | Topic |
| Lecture 1 (Tue Feb 6) | Quantum bootcamp + the Wiesner money scheme [Lecture Notes] |
| Lecture 2 (Thu Feb 8) |
Attacks on Wiesner: cloning, Lutomirski's attack, Quantum Zeno Effect and the Elitzur-Vaidman bomb [Lecture Notes]
References: |
| Lecture 3 (Tue Feb 13) | Canceled due to "snowstorm" |
| Lecture 4 (Thu Feb 15) |
BB84 key exchange and security sketch
References:
|
|
Tue Feb 20 Monday Schedule of Classes |
|
| Lecture 5 (Thu Feb 22) |
Symmetric subspace and de Finetti theorem
References:
|
| Lecture 6 (Tue Feb 27) |
BB84 Security Analysis Concluded: Information
Reconciliation, Privacy Amplification, and Uncertainty
References:
|
| Lecture 7 (Thu Feb 29) |
Beyond BB84: Impossibility of Quantum Bit Commitment/ Uhlmann's theorem
References:
|
|
Lecture 8 (Tue Mar 5) |
Post-quantum Security 1: Pseudo-random Functions, Collapse-Binding [Lecture Notes]
References:
|
|
Lecture 9 (Thu Mar 7) |
Post-quantum Security 2: Collapse-Binding (Contd.) and Its Applications
References:
|
| Lecture 10 (Tue Mar 12) |
Jordan Lemma, Watrous Rewinding and Zero Knowledge against Quantum Attacks
References:
|
| Lecture 11 (Thu Mar 14) | Rewinding and Zero-Knowledge (continued) Guest Lecturer: Alex Lombardi |
|
Lecture 12 (Tue Mar 19) |
Commitments and Oblivious Transfer from One-way Functions
References:
|
|
Lecture 13 (Thu Mar 21) |
Pseudorandom Quantum States (PRS): definition and construction
Guest Lecturer: Alex Poremba [Lecture Notes]
References:
|
| Tue Mar 26 Spring Break | |
| Thu Mar 28 Spring Break | |
| Lecture 14 (Tue Apr 2) |
Commitments from PRS, and oracle PRSs from weak assumptions
Guest Lecturer: Luowen Qian [Lecture Notes]
References:
|
|
Lecture 15 (Thu Apr 4) |
Lattices, Gaussians and Shor Factoring [Lecture Notes]
References:
|
| Lecture 16 (Tue Apr 9) |
Regev's Algorithm for Factoring.
Guest Lecturer: Seyoon Ragavan
References:
|
|
Lecture 17 (Thu Apr 11) |
Regev's worst-case to average-case reduction
References:
|
| Lecture 18 (Tue Apr 16) |
Yamakawa-Zhandry Proof of Quantumness.
References:
|
|
Lecture 19 (Thu Apr 18) |
Trapdoor Claw-free Functions and the BCMVV Proof of Quantumness
References:
|
|
Lecture 20 (Tue Apr 23) |
Quantum FHE and the CHSH Protocol
References:
|
|
Lecture 21 (Thu Apr 25) |
Proofs of Quantumness: Extracting and measuring a qubit
References:
|
|
Lecture 22 (Tue Apr 30) |
Testing multiqubit measurements: Pauli braiding + Gowers-Hatami
References:
|
| Lecture 23 (Thu May 2) |
Delegation and Remote State Preparation
Guest Lecturer: Andru Gheorghiu
References:
|
|
Lecture 24 (Tue May 7) |
Uncloneable Cryptography
Guest Lecturer: Jiahui Liu
References:
|
|
Lecture 25 (Thu May 9) |
Student Presentations |
| Lecture 26 (Tue May 14) | Student Presentations |
Resources (Quantum Information and Computation)
- MIT 8.370 Quantum Computation Lecture notes.
- MIT 8.S372/18.S996 Quantum Information Science 3. Lecture notes are available here.